Account Takeover Detection and Effective Ways of Preventing It
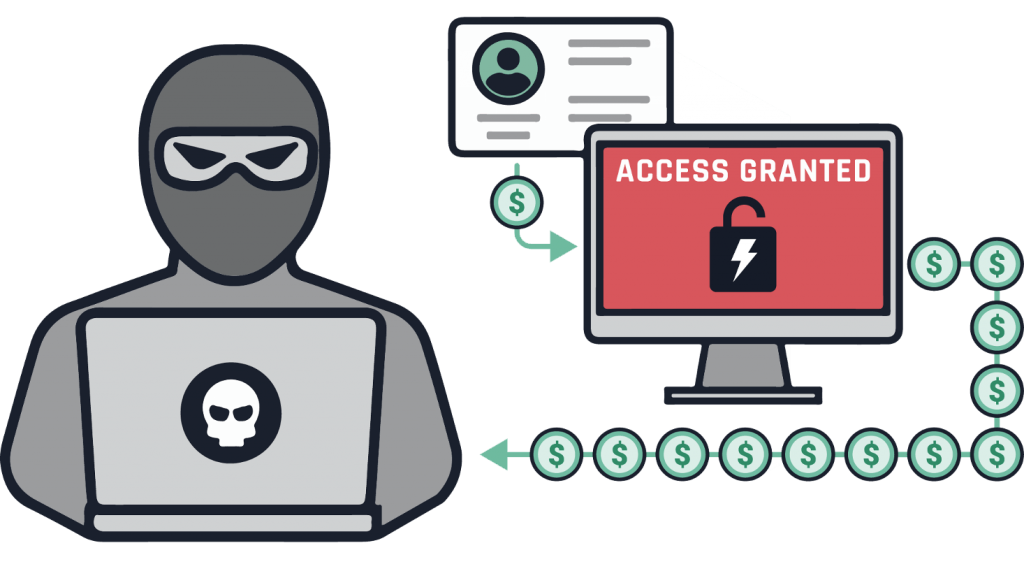
Account takeover is a kind of identity fraud where unauthorized users steal passwords and other credentials to access sensitive information in an organization. Some of the hotspot industries of account takeover are hospitality, retail, finance, and media. Criminals use the stolen credentials to log into the accounts without express authority and exploit, affecting the company’s stability and reputation.
Account takeover is becoming very attractive to fraudsters because these days, people do almost everything on the internet. That is why the fraudsters know that they can access a lot of information for individuals and organizations through account takeover attacks.
The fraudsters also know that apps do not only have access to a single piece of information. For instance, if you gain access to card information, you can also access much more private information. Knowing how to detect and prevent account takeover attacks prevents fraudsters from accessing sensitive data and protects their reputation. Here are some of the common account takeover possibilities and how to catch them before they happen.
Multiple Changes of Account Details
Fraudsters are very canning these days, and they want to use existing accounts to make it easy for them to access information fraudulently. They target to claim an existing account so that no one else can claim it. One way they achieve that is to change several account information by changing details on a genuine customer profile. They only change the information that will benefit them, and they can leave the rest of the information as they were before. In that case, you may notice massive changes in contact telephone numbers across a considerable number of accounts.
When you see an enormous change in information, it will be prudent to investigate. You may be surprised to find that the customers are changing to the same telephone number, which is an indication that someone is stealing the identity. The telephone number most likely belongs to a fraudster.
Phishing Attack
The most common account security attacks happen during phishing, where attackers pose themselves as legit organizations. They then use that organization’s name to ask for identifiable information from either an individual or a company. They trick the recipient of either the phone call or email, or text messages into taking action and exposing data to the wrong people. They can use that trick to get information about the geographical location IP address, passport number, among others.
You can detect that you provide information to the wrong people when you see a generic greeting on the email or text message. They begin with a “hi there” greeting instead of using your name. Also, the fraudsters ask you to complete an action immediately so that you do not have time to think. When you see emails leading to a separate page than the writer’s claims or the URL does not begin with HTTPS, you are most likely dealing with a fraudster. Before giving any sensitive information, it is essential to verify the caller to become a victim of an account takeover attack.
Brute Force Attack
Fraudsters conduct brute force attacks when targeting large businesses. They use automated bots to check and identify valid credentials and crack password codes and log into accounts. You can suspect an account takeover when you find several login attempts in a single account. Also, you can find failed testing attempts where the person login in is using multiple account ids and passwords. Sometimes you may see a bill that has exponential account locks for cases of hijacked accounts.
How to prevent Account Takeover
There are several reasonable account takeover practices that every business should deploy to protect their businesses.
1. Use Multi-Factor Authentication
Multi-factor authentication also referred to as MFA, is an additional; layer of security to your business. It uses an authentication code, fingerprint or retina scan when login into an account. Once you see the verification code or whatever you are using for verification, you will lock out any other person from accessing the account. No one will be able to log in unless they have the verification code.
2. Teach Your Staff How to Recognize and Report Attacks
When you train your staff, they will have the capacity to note possible attacks and report before something harsh happens to your business. Simulated phishing attacks for voicemails, emails, and text messages are very effective tools for training your staff. That will ensure the employees can recognize the attacks, understand how they can use them on fraudulent transactions, and report them.
3. Protect your Online Environment
Protecting your online environment is essential, and therefore, you should avoid anything that can cause account takeover fraudulent activity. Ensure that you use protected internet connections and also encrypt any sensitive data. Also, make sure you update the virus protection on your device and incorporate complex passwords.
4. Partner with Your Bank
It is essential to work hand in hand with your bankers to ensure no fraudulent activities occur in your account. You can protect your account from any fraudulent transaction if your bank employs a program to safeguard you from unauthorized transactions. Your bank should use call bank as one of the best practices to avoid unauthorized huge sums transactions.
5. Act Fast
You need to pay attention to any suspicious activity and ask fast when you suspect anything. Look out for unexplained accounts or network activity, pop-ups, suspicious emails. Once you note something that looks suspicious, it is important to act very fast to stop any action.
6. Malware or Replay Attacks
Malware attacks present a particular challenge because the attacker compromises the machine. The attackers use malware to capture consumer login credentials and link the information to other attackers. The attackers may also capture and manipulate data the attacker compromises the machine and transmit it. For instance, a fraudster may use a request to view a page and change it to a request for wire transfer.
You can detect the malware account takeover attacks when you receive customer complaints about fund transfers that they have not authorized. You may also notice valid user identifications being used to conduct unauthorized activities.
Conclusion
It is better to do everything possible to protect your business from account takeover attacks. You may think that you are overspending on the protection measures, but it pays in the end. Therefore you should make sure your business is well protected by using the most effective protection tools. The methods stated above are some of the most effective tricks on account takeover attacks, but there are many more. It is essential to do everything you can to protect your business, as account takeover attacks can ruin your business reputation.